Unified findings pipeline
Every tool, parser and reviewer writes to one per-client findings store with CVSS scoring, evidence capture and remediation text ready for report generation.
Self-hosted · Kali-native · Job-driven
90+ integrated tools, a unified findings pipeline, and automated reports. Built by pentesters, for pentesters.
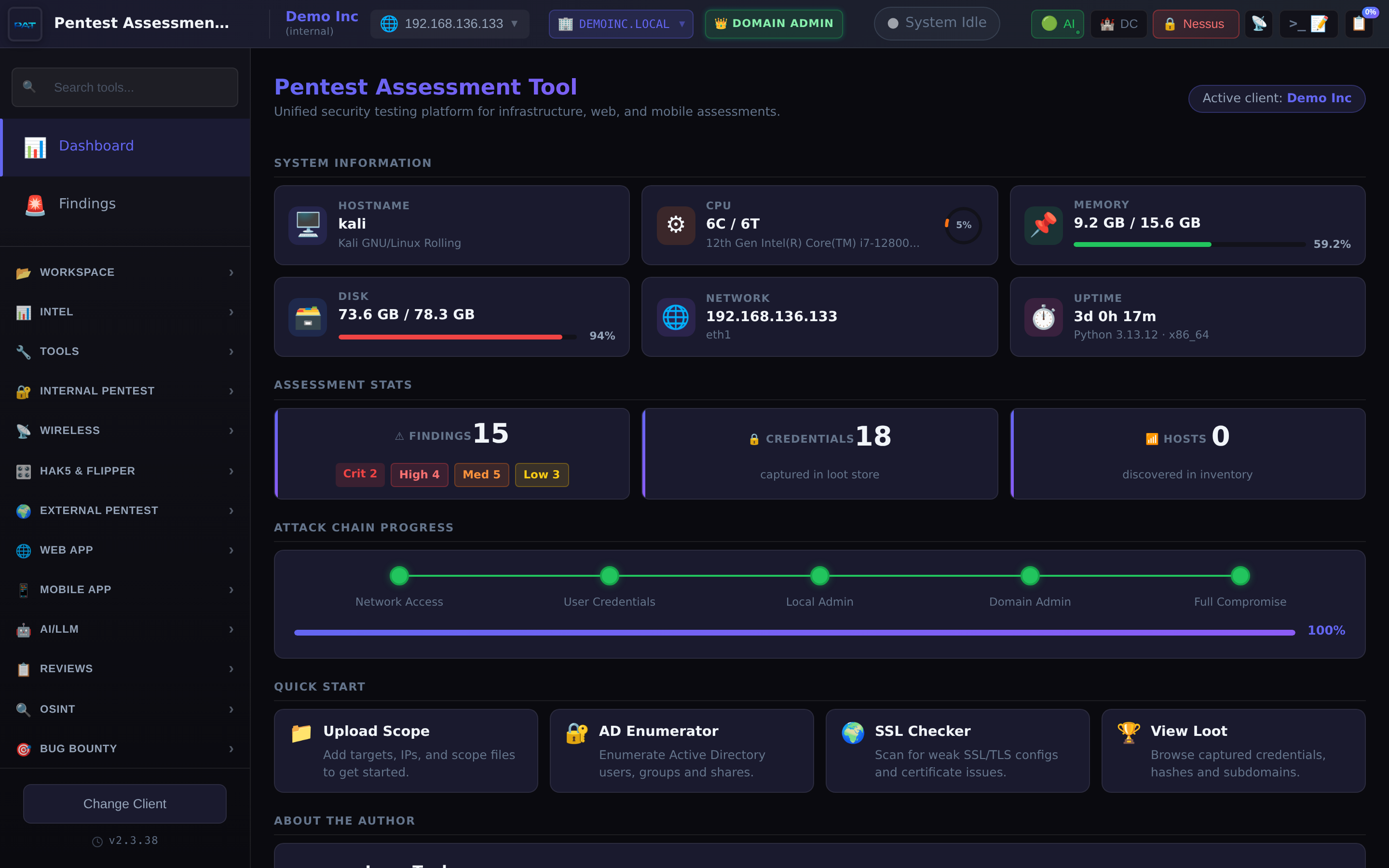
A curated stack of reconnaissance, exploitation, review and reporting tooling, all writing to a single per-client workspace.
Every tool, parser and reviewer writes to one per-client findings store with CVSS scoring, evidence capture and remediation text ready for report generation.
Kill-chain graph with MITRE ATT&CK mapping, auto-generated from credentials, hosts and compromise state. Fully editable for manual attack narratives.
Palo Alto, Cisco IOS, ASA, FortiGate, Juniper ScreenOS and JunOS, Check Point, SonicWall and pfSense. Plus Titania Nipper v2/v3 XML import to reuse prior audits without re-analysis.
Nessus, Burp Suite Pro, BloodHound, Nmap XML, MobSF, Office 365 scan output, IART finding library. Data flows into the same unified pipeline.
Every long-running tool runs as a cancellable background job with live terminal streaming, PID tracking, completion events and per-client history.
Executive summary, scope table, findings by severity, evidence tables, auto-populated host tables. Generated from a template that keeps the professional voice consistent across engagements.
A tour of the tool. All content shown is synthetic: screenshots are captured against a fictional “Demo Inc” client populated from static fixture data.
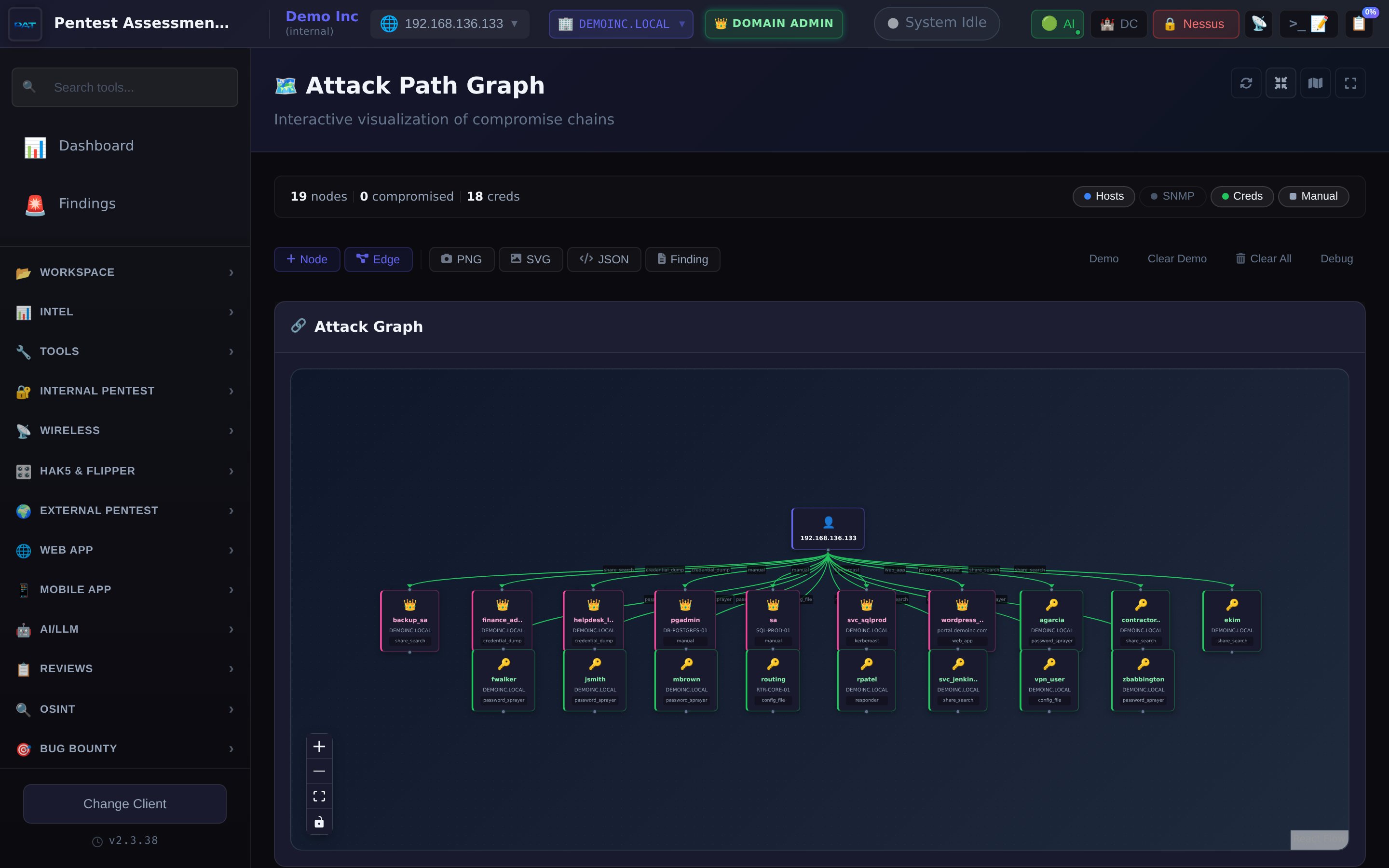
Kill-chain visualisation with MITRE mapping.
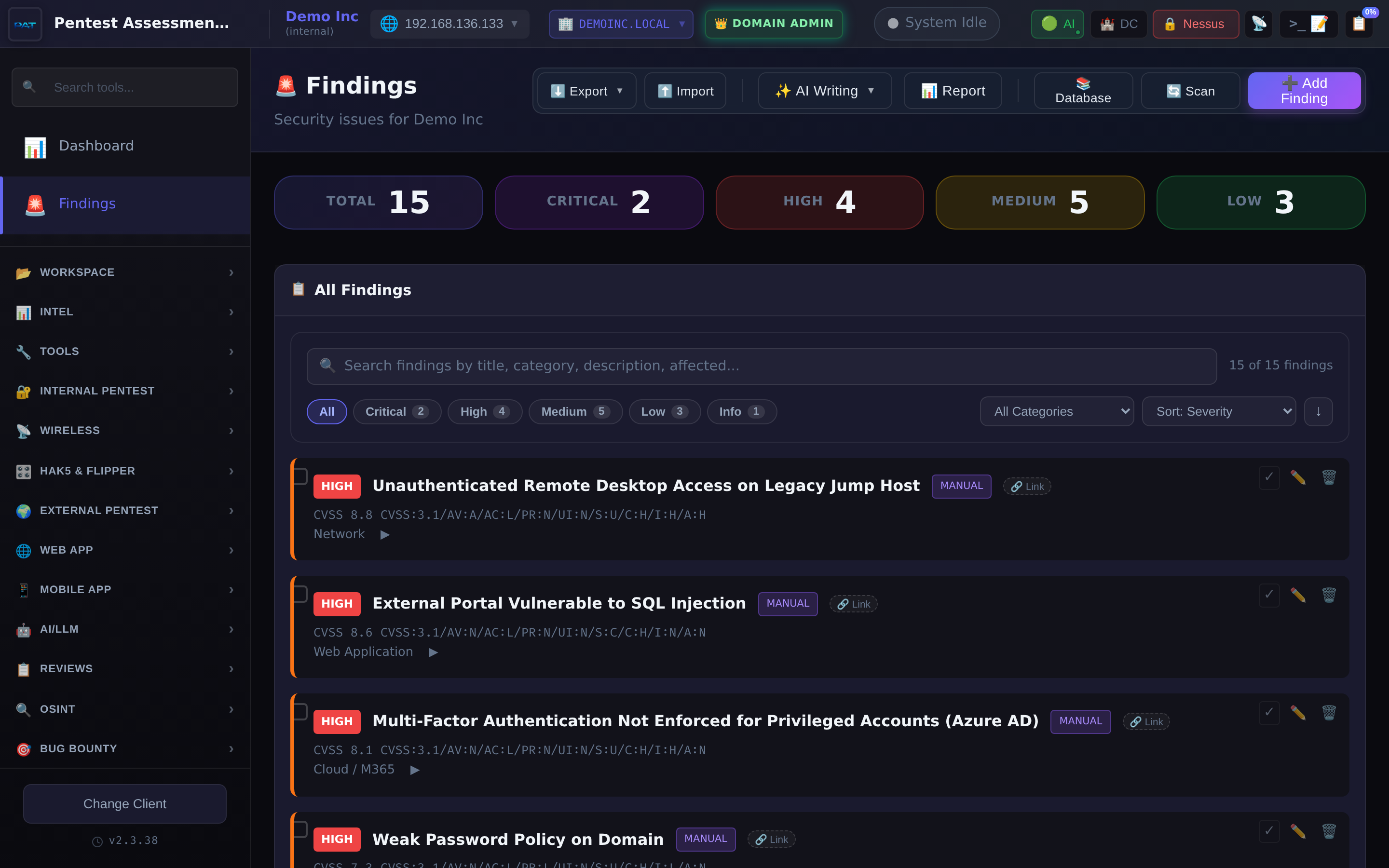
The deliverable. CVSS, evidence, remediation.
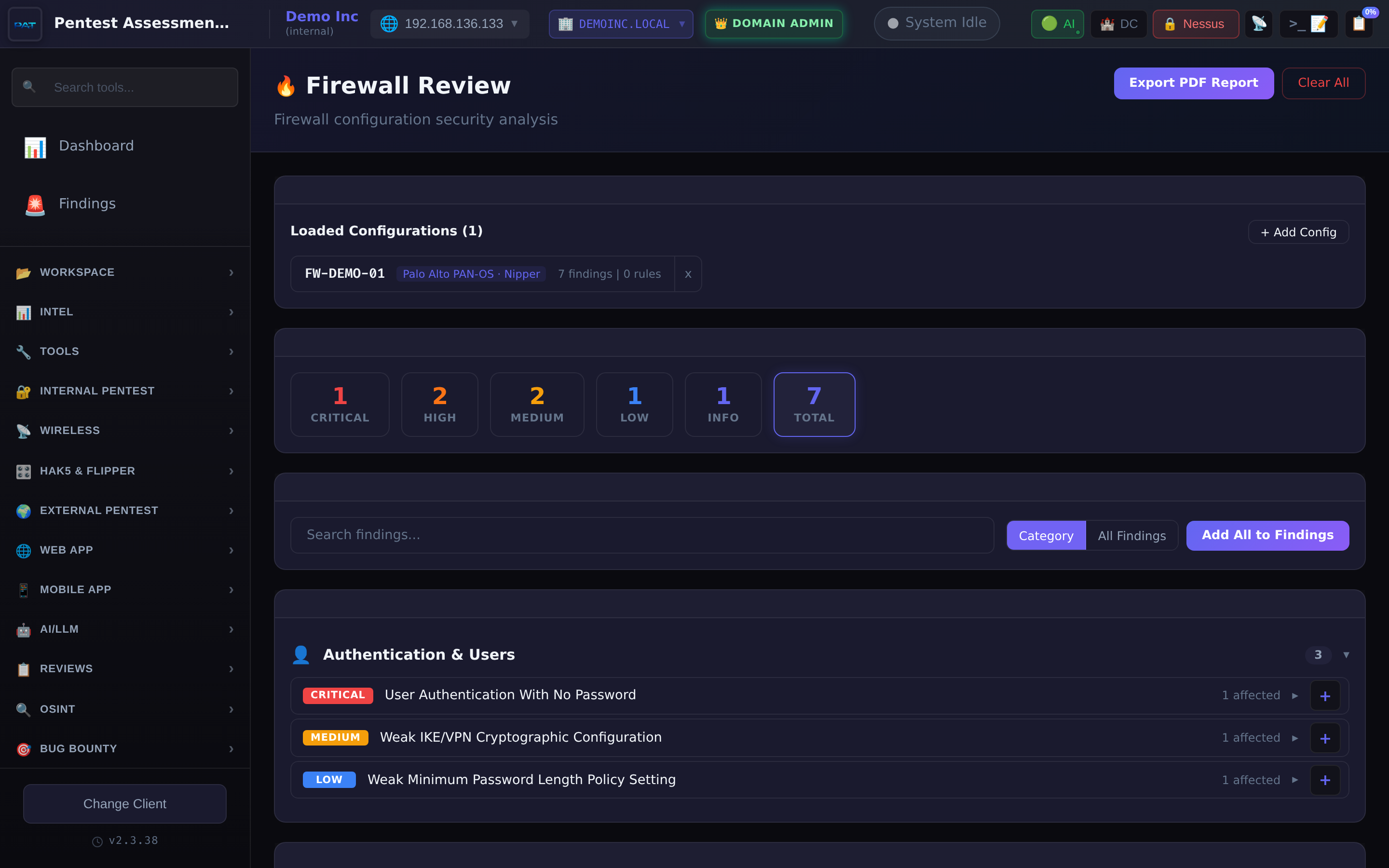
Nine-vendor parser plus Nipper v2/v3 import.
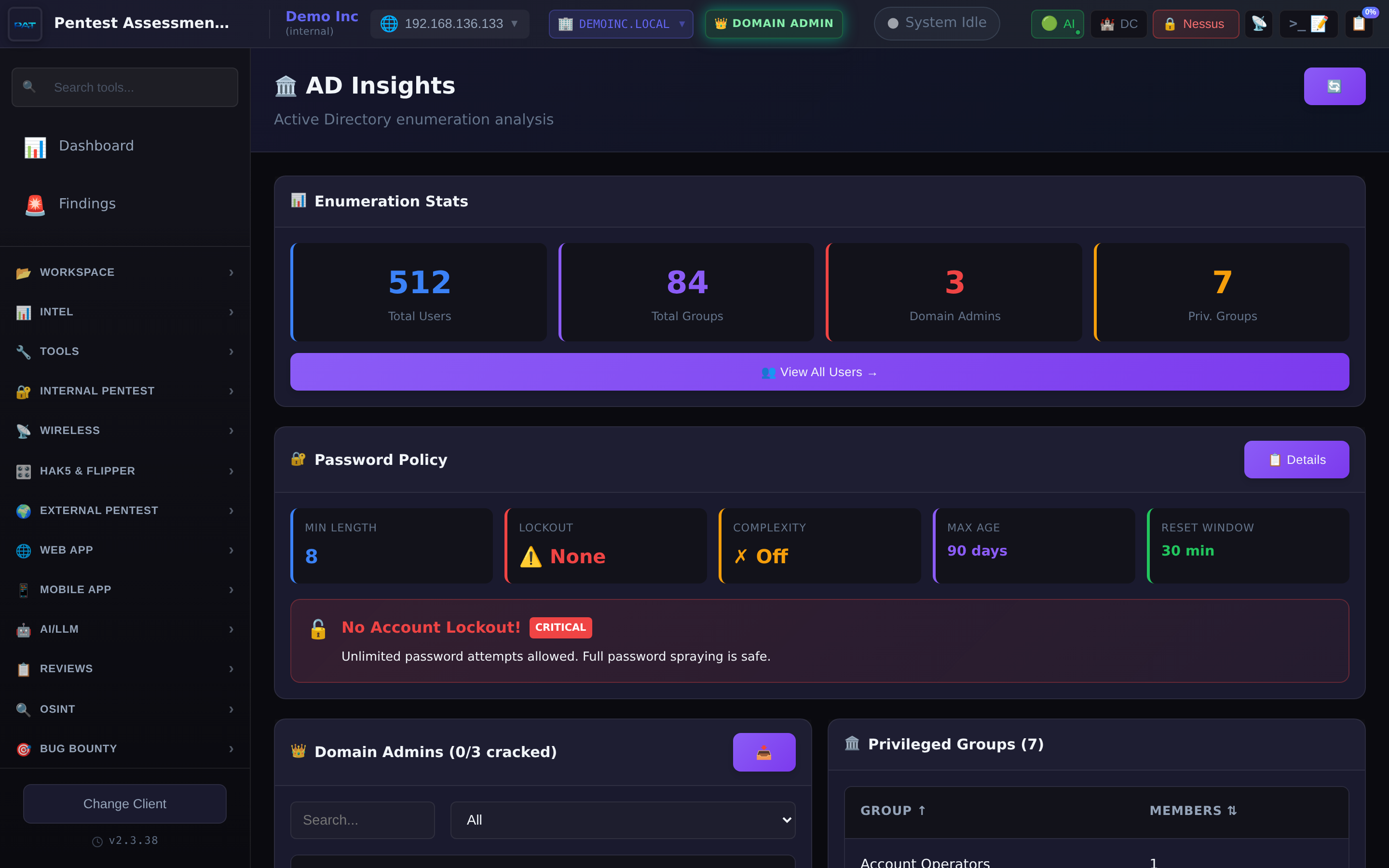
Domain admin exposure, privileged groups, password policy.
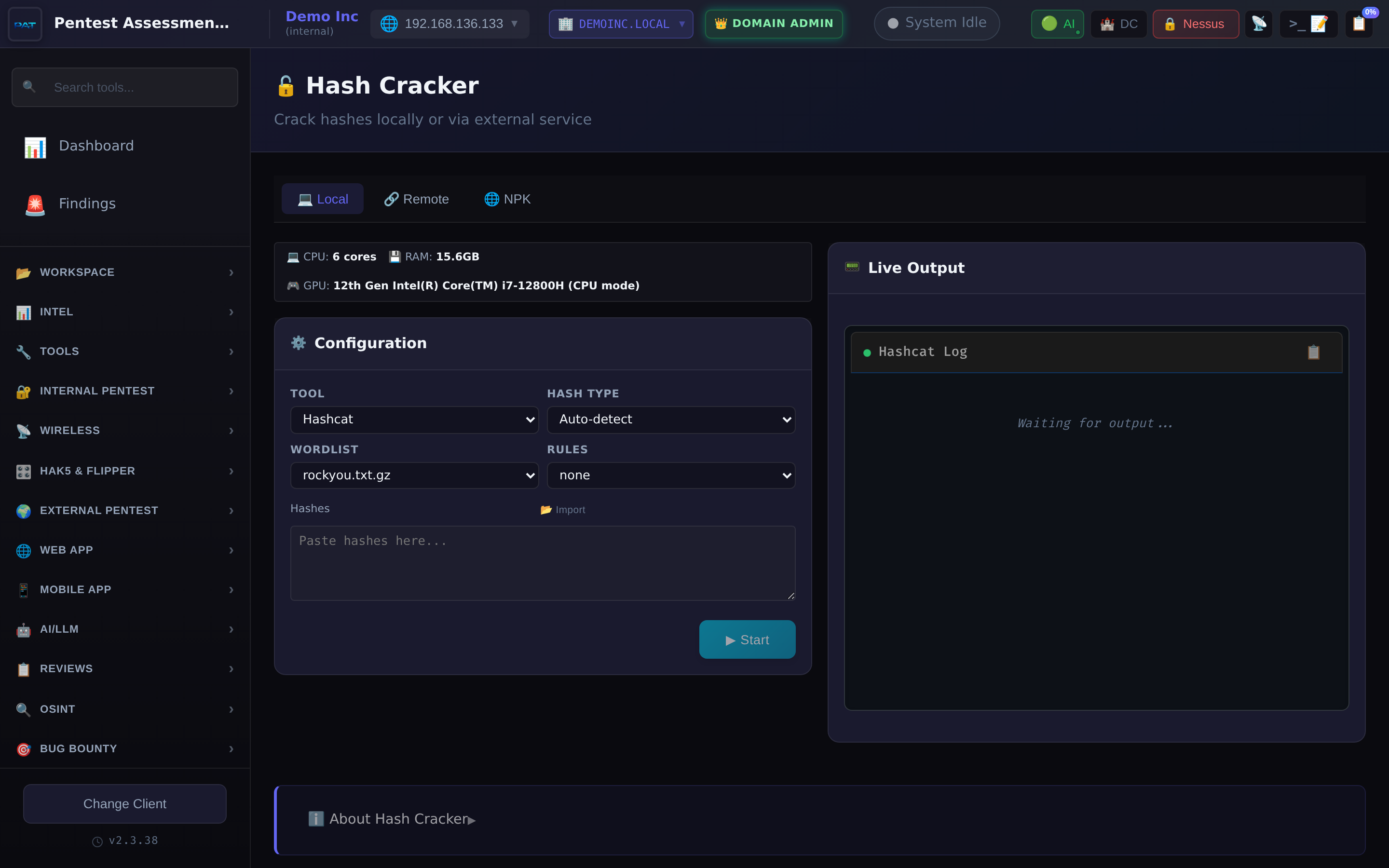
Hashcat and John with live terminal streaming.
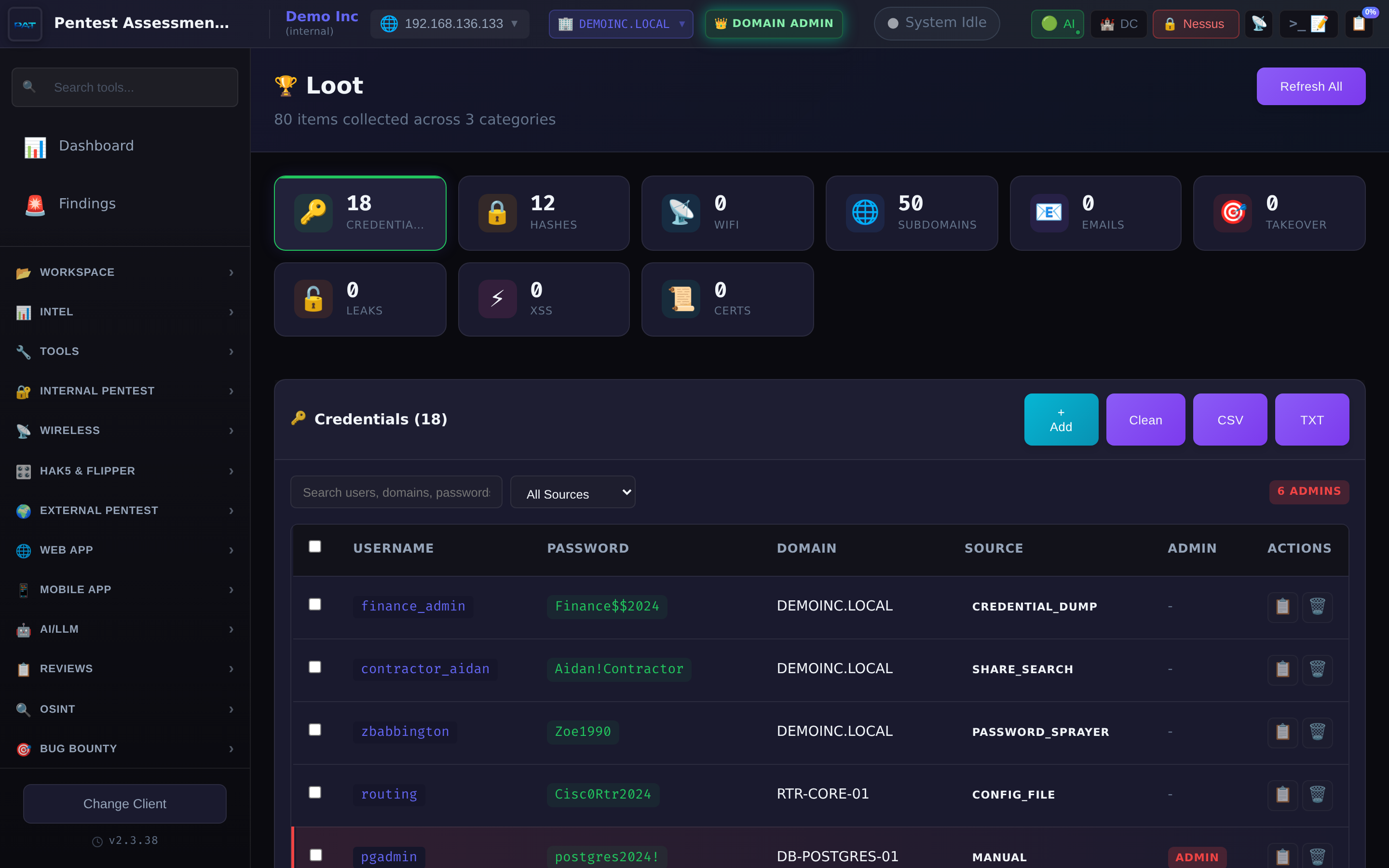
Credentials, hashes, subdomains, emails, certificates.
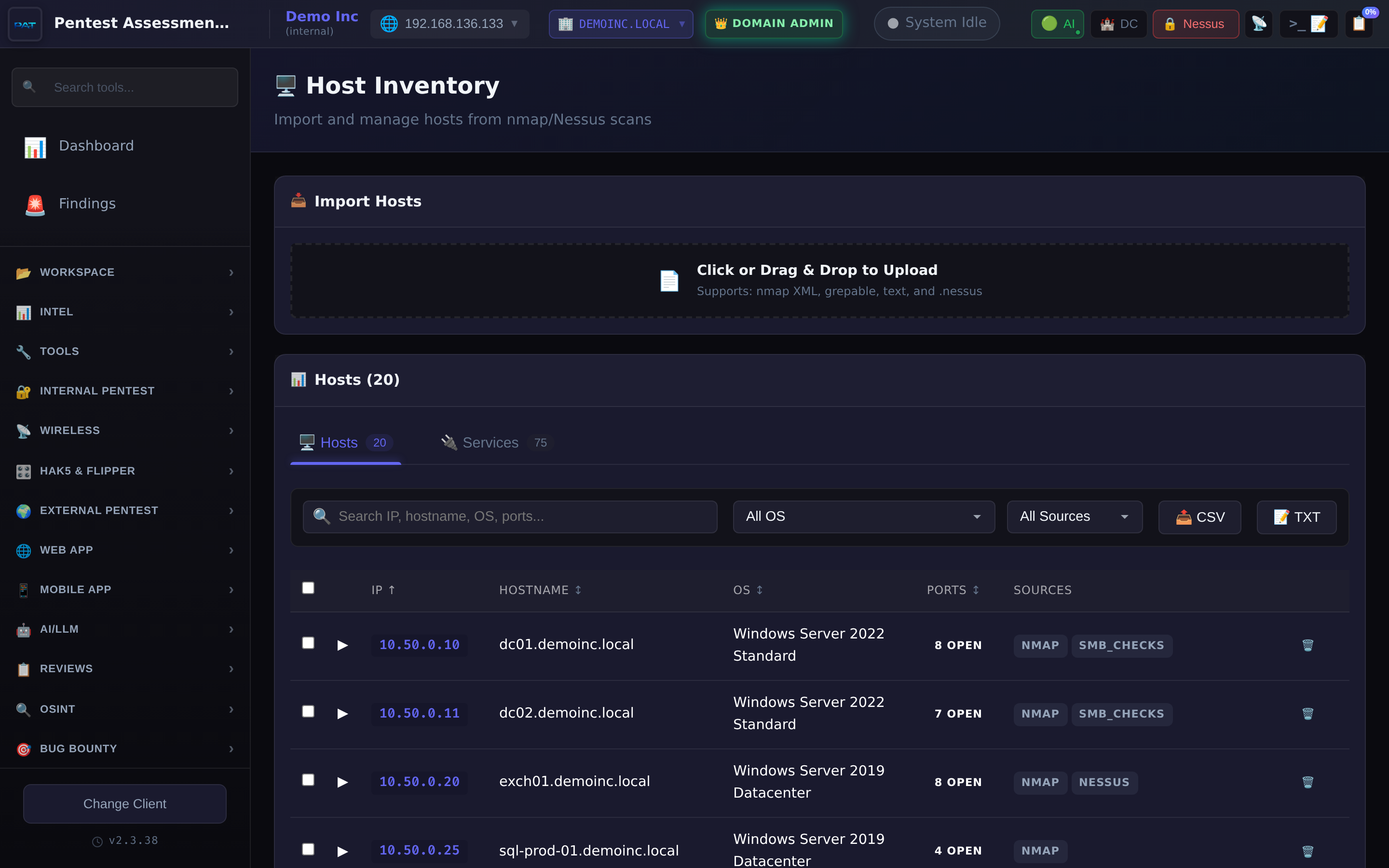
Unified inventory from Nmap, Nessus and manual input.
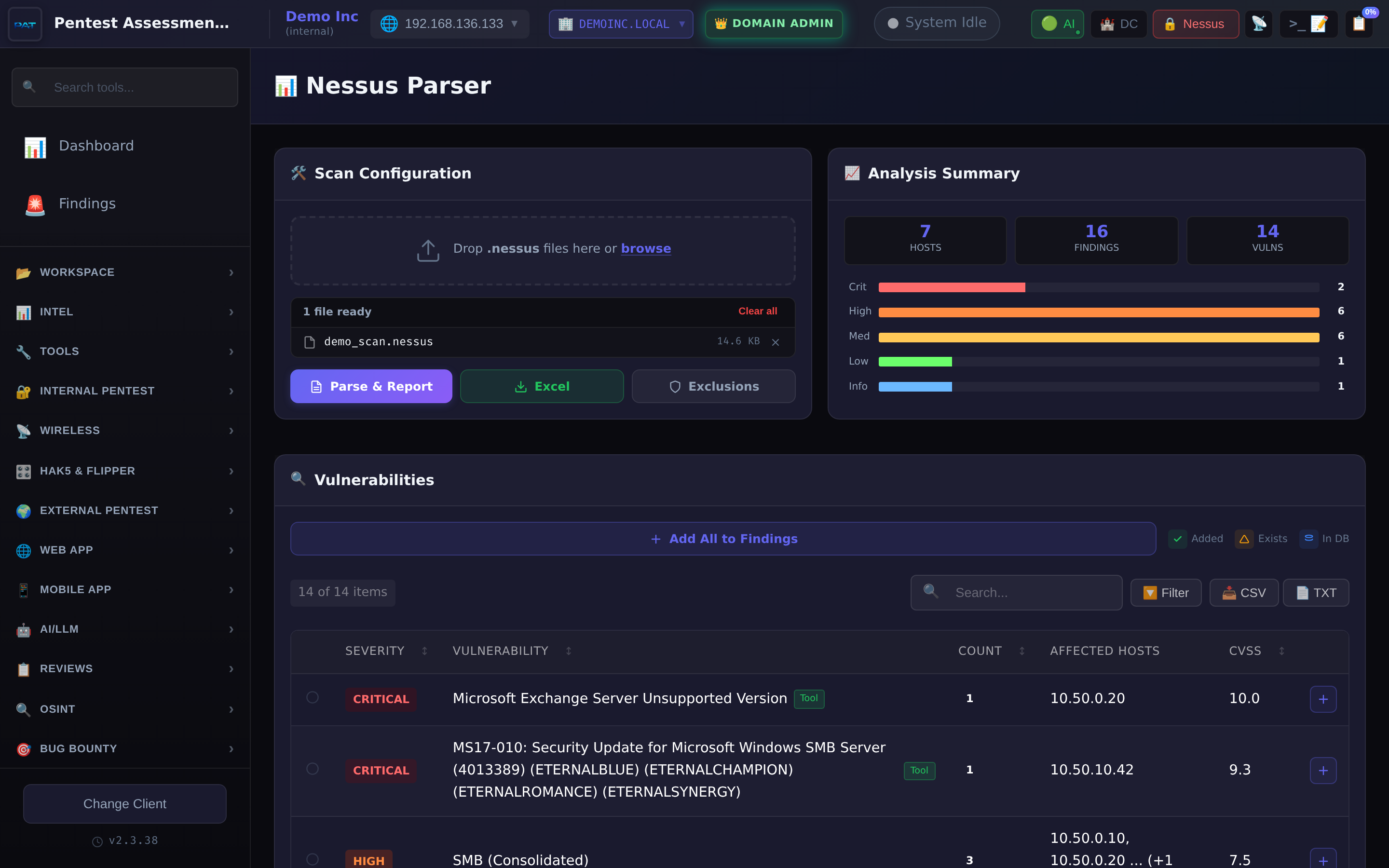
Ingest .nessus scans, triage by severity, auto-file findings.
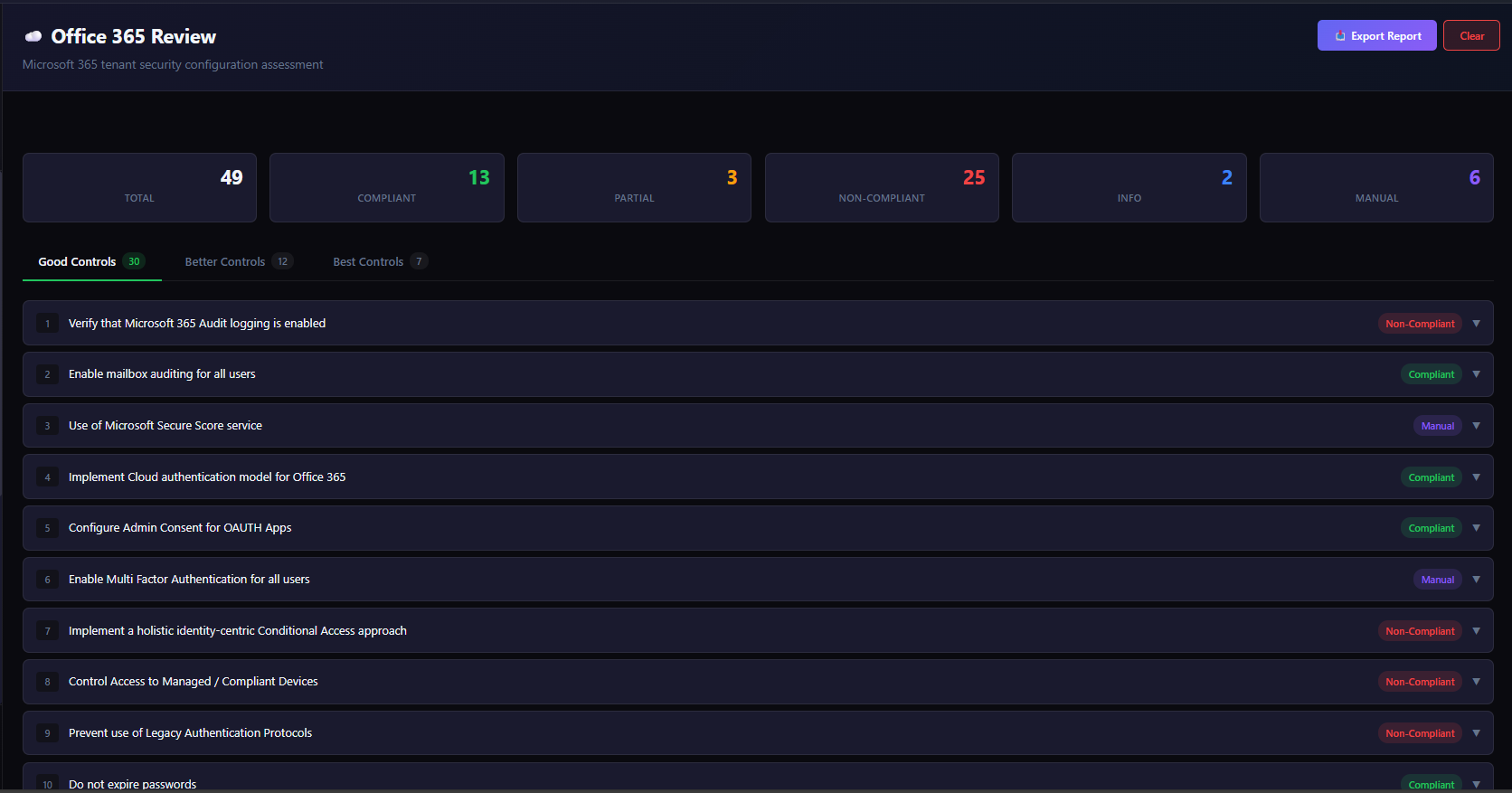
Tenant security posture across 49 compliance checks.
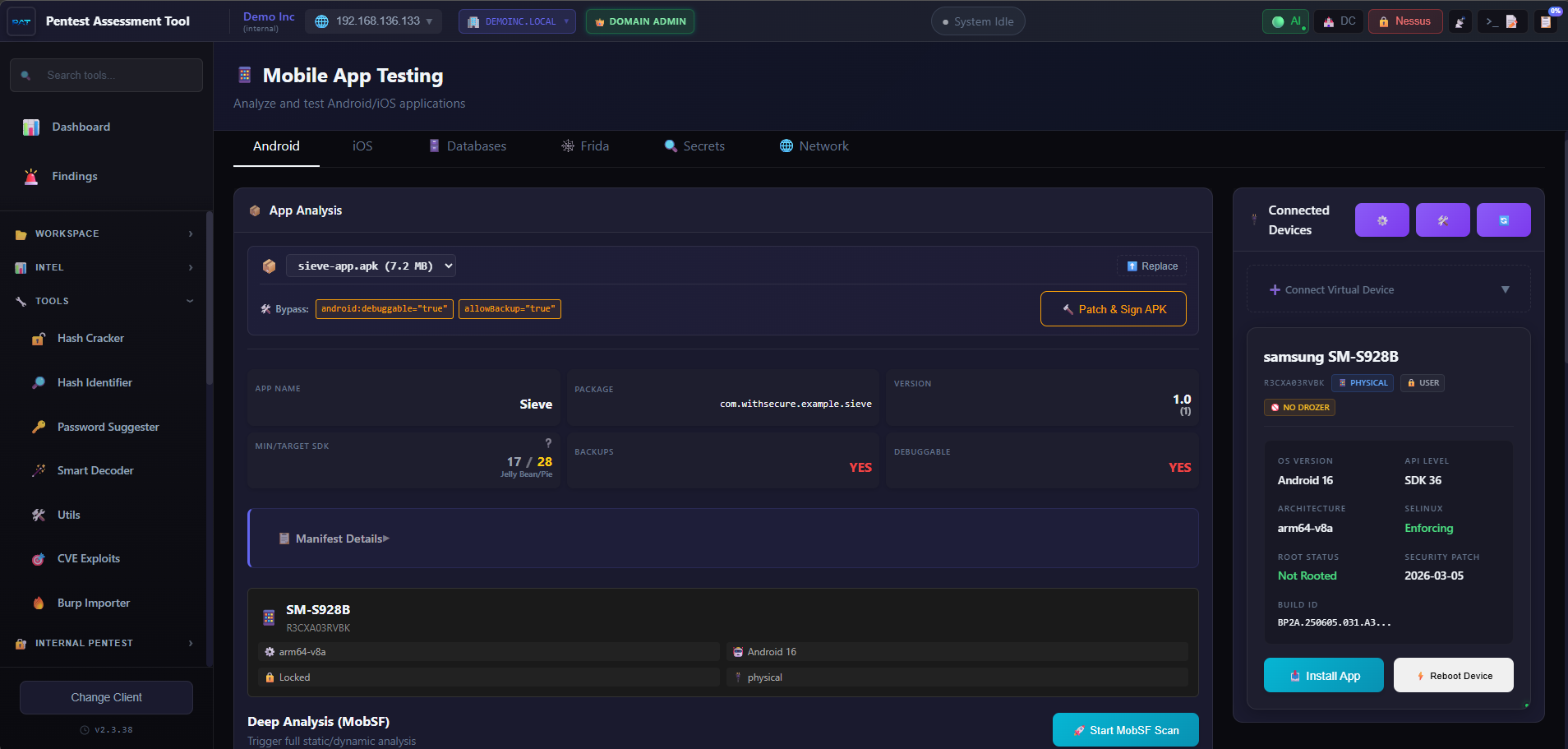
MobSF, ADB and Drozer side by side.
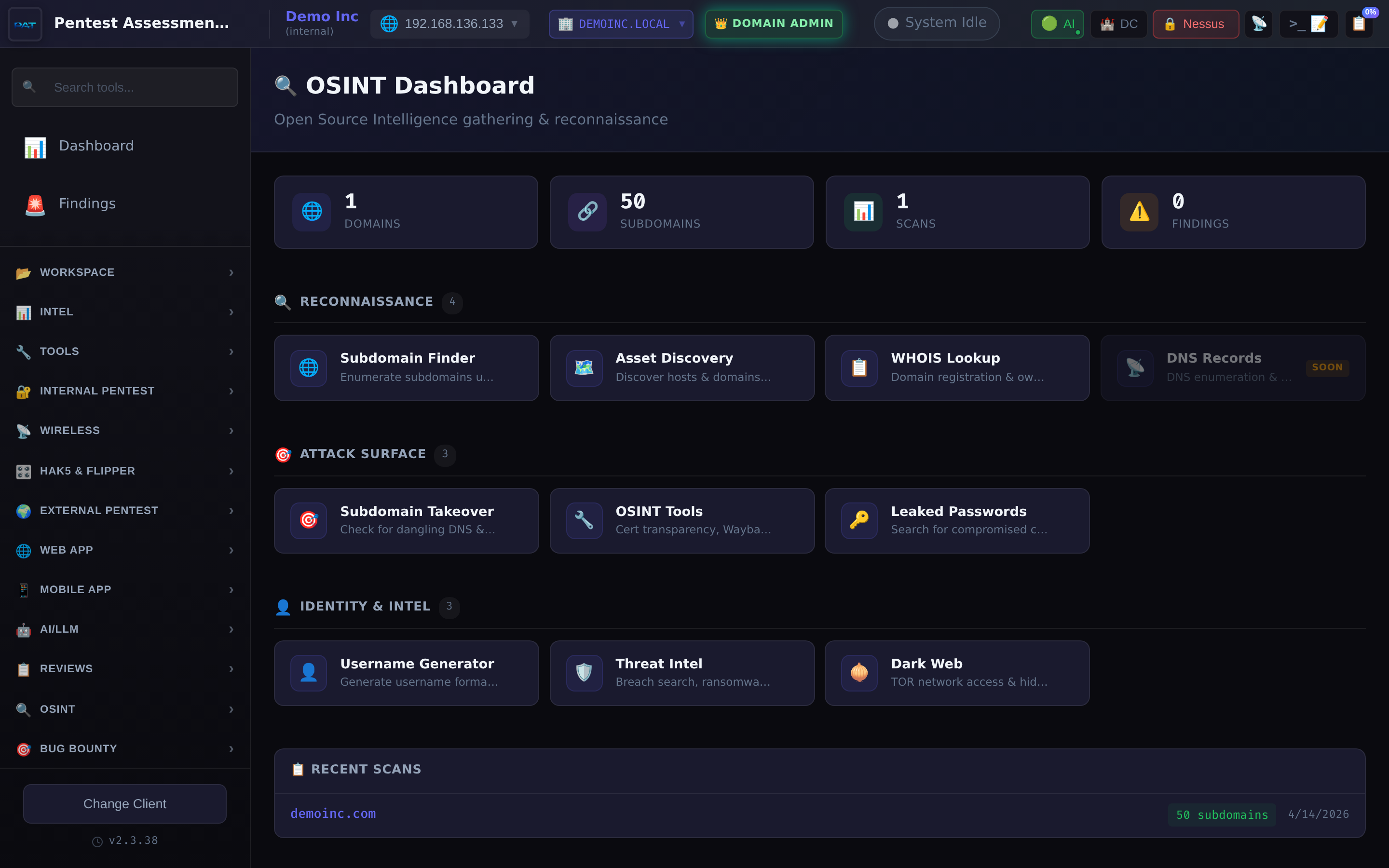
Subdomains, takeover candidates, discovered assets.
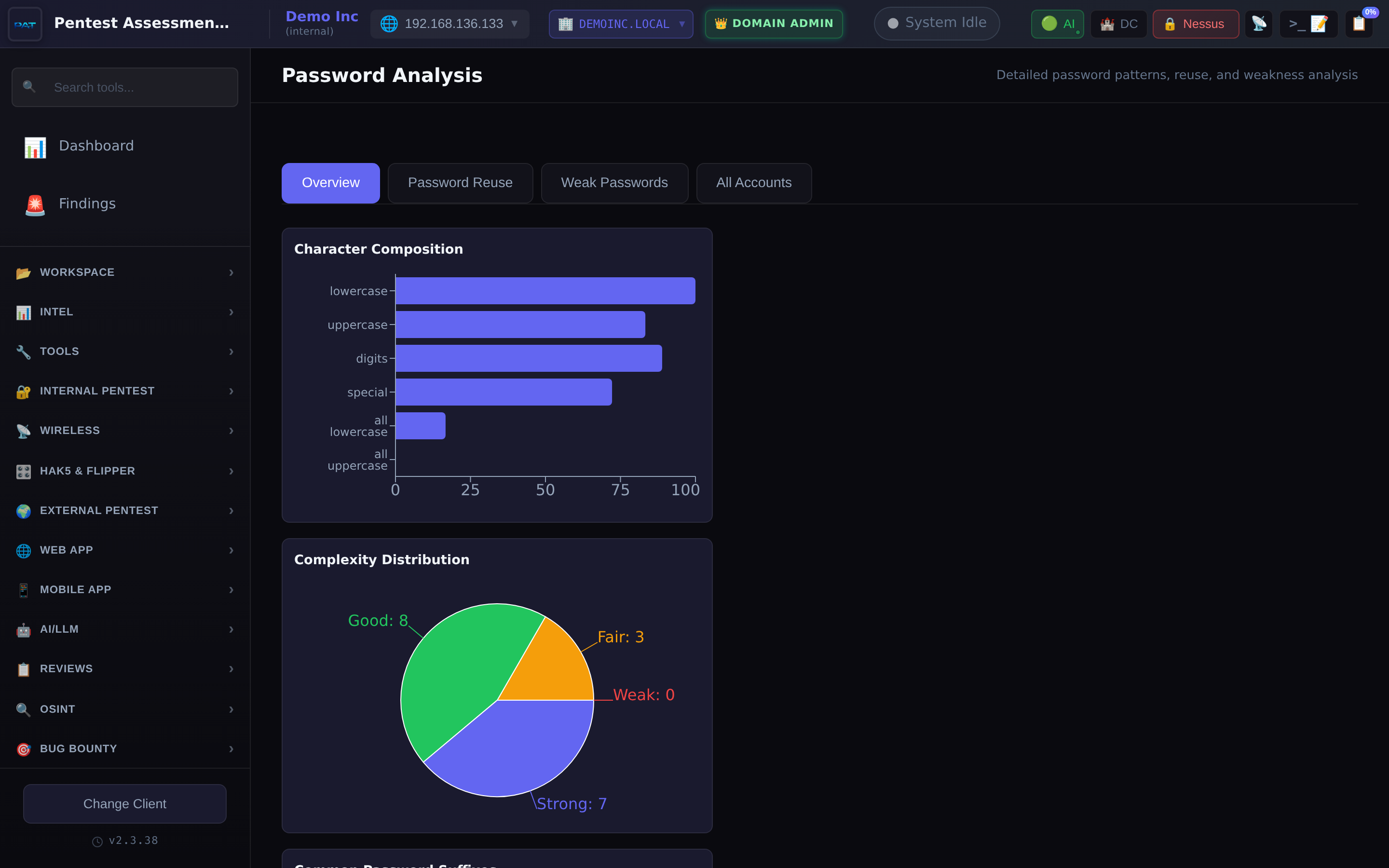
Length histogram, reuse percentage, top patterns.
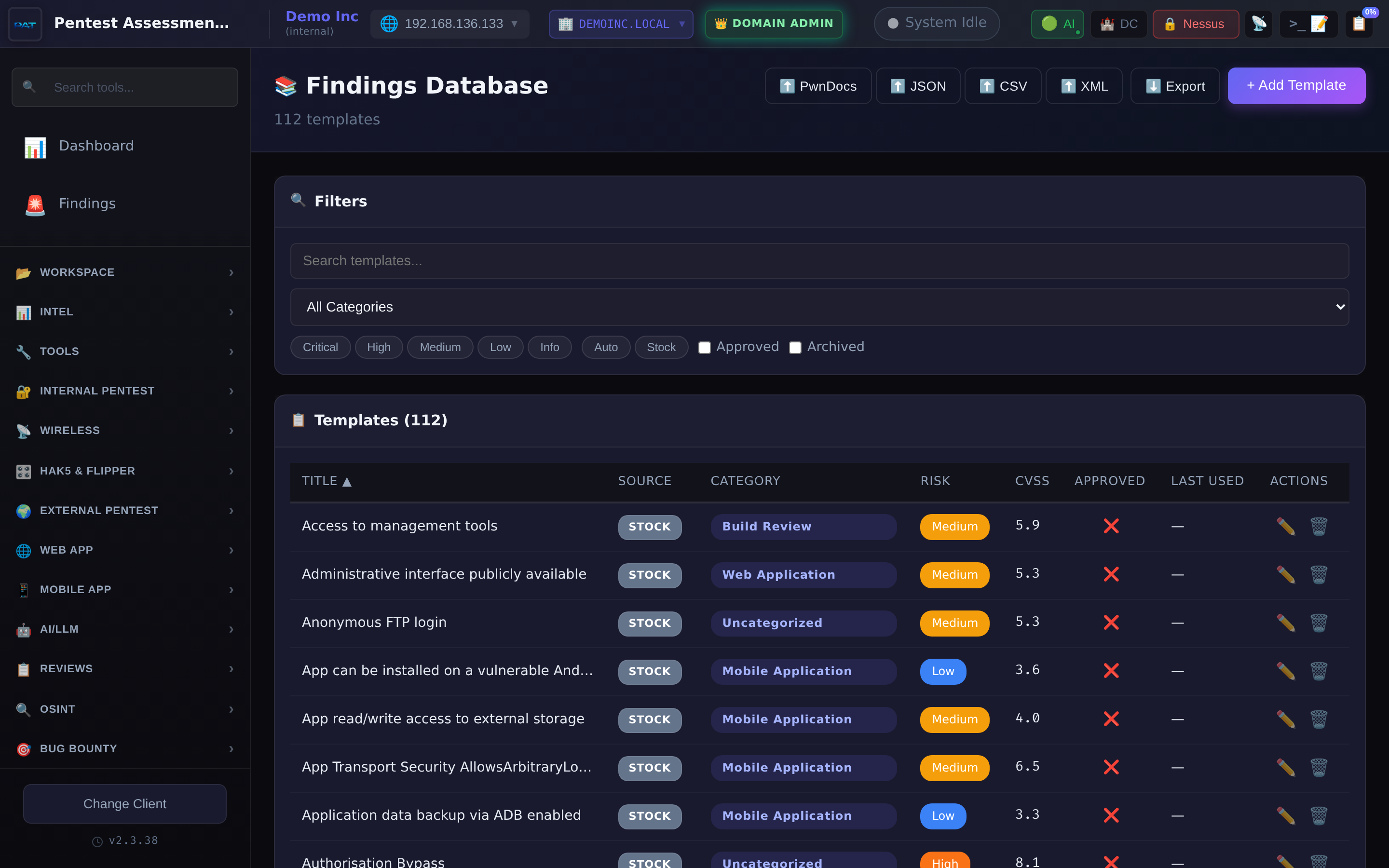
Reusable template library with IART import.
The tool is built against Kali Linux and expects its default tool paths and wordlists. Other distributions may work but are not supported.
Clones the repository, installs the Python backend and Node frontend dependencies, builds the Vite bundle, and pins tool versions.
git clone https://github.com/leonteale/Pentest-Assessment-Tool.git
cd Pentest-Assessment-Tool
./setup.shBrings up the FastAPI backend on port 8000 and the Vite frontend on 5173. Open the browser, create your first client, and start ingesting.
./start.sh
# Backend: http://localhost:8000
# Frontend: http://localhost:5173Release history, latest first.
The tool is source-available on GitHub. Clone the repository,
run ./setup.sh, then ./start.sh.